SmartX has announced the addition of a new Network and Security component to its hyper-converged infrastructure (HCI). With micro-segmentation at its core, the new component aims to help customers secure east-west traffic in various virtualization scenarios, enhance network security inside data centers, and build “zero trust” enterprise cloud infrastructure.
As the foundation for data center interconnection, the network is facing increasingly severe internal and external security threats. Given the fact that, on one side, traditional data center network security mainly focuses on perimeter protection, thus unable to guarantee the trustworthiness and security of lateral access inside the data center; on the other side, the legacy network segmentation inherently requires complex management configuration. In response, “micro-segmentation” is emerging as a network architecture based on the “zero trust” concept, offering granular network isolation.
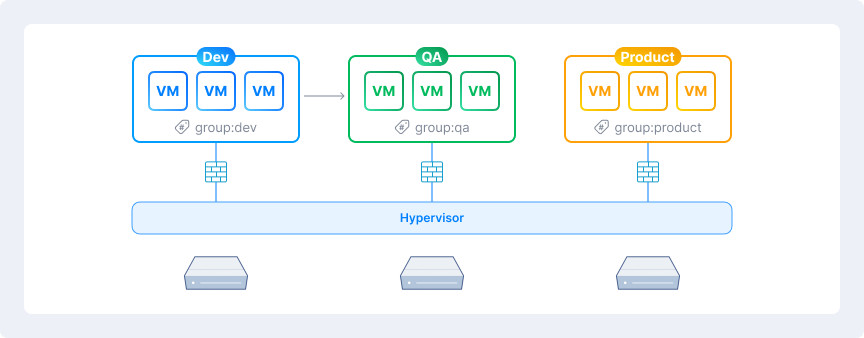
SMTX micro-segmentation is built on Kubernetes cloud-native framework and could be centrally orchestrated. Based on SMTX OS Virtual Distributed Switches, micro-segmentation supports three types of distributed firewall policies, namely virtual machine isolation, network security policy, and global policy. It matches the requirements of “zero trust” architecture.
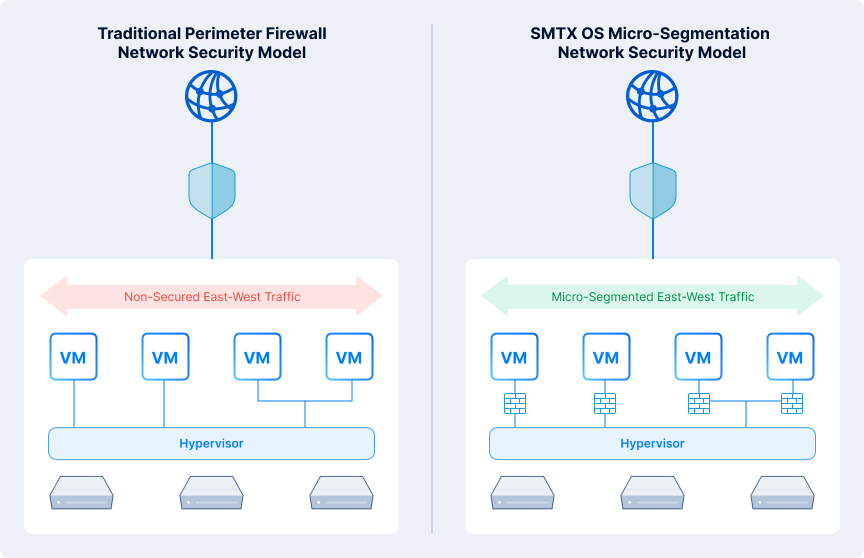
With the micro-segmentation function of the Network and Security component applied, the data center is still isolated from the outside by the perimeter firewall. Inside the data center, each virtual machine built on SmartX HCI is protected by distributed firewall rules. The features of SMTX OS Network and Security component are listed below:
- Network Micro-Segmentation: VMs are easily grouped by application labels. Granular security policies for VM are applied to granular network segments. Inter/inner segments traffic is granted with least privilege access.
- On-Demand Isolation or Diagnostics: Completely isolate infected virtual machines in time, blocking malicious attacks from spreading inside the data center; furthermore, set virtual machines into “diagnostic isolation” mode for debugging.
- Sticky Policies: Security policies are always associated with virtual machines along the whole lifecycle, even with the migration, IP/MAC changing, label re-association or HA failover of the VM.
Micro-segmentation inside the data center offers the following advantages when compared to the legacy network segmentation:
- Easy-to-Use
○ No plug-in needed, VM labeling and grouping are handled by hypervisor, IP addresses of VM are automatically mapped with its group labels and security policies. The auto-correlation simplifies the implementation of security.
○ Declarative API, leaving users to focus solely on realizing the expected results, with no concern about the intermediate process.
○ No need to modify the configuration of switching, routing, security etc., on a physical network.
- Scalability
○ Adopt distributed firewall architecture, with scale-out capability.
○ Support unified network security policy management for multiple SMTX OS clusters.
○ Support unified network security policy management for multiple clusters across data centers.
- High Availability
○ High availability cluster composed of multiple controller instances, eliminating any single point of failure.
○ Control plane failure does not stop forwarding on the data plane.
- Wide Compatibility
○ Support arbitrary underlying network architecture, independent of any physical network equipment, regardless of brands, models, or feature sets.
○ A software-based implementation, independent of any hardware (e.g. servers, NICs); support mixed deployment on multiple architectural platforms, including x86, Hygon, ARM, etc.
With the embedded Network and Security component, SmartX HCI products can meet the core requirements of business-driven digital transformation in enterprise architecture on network security. The key use cases include:
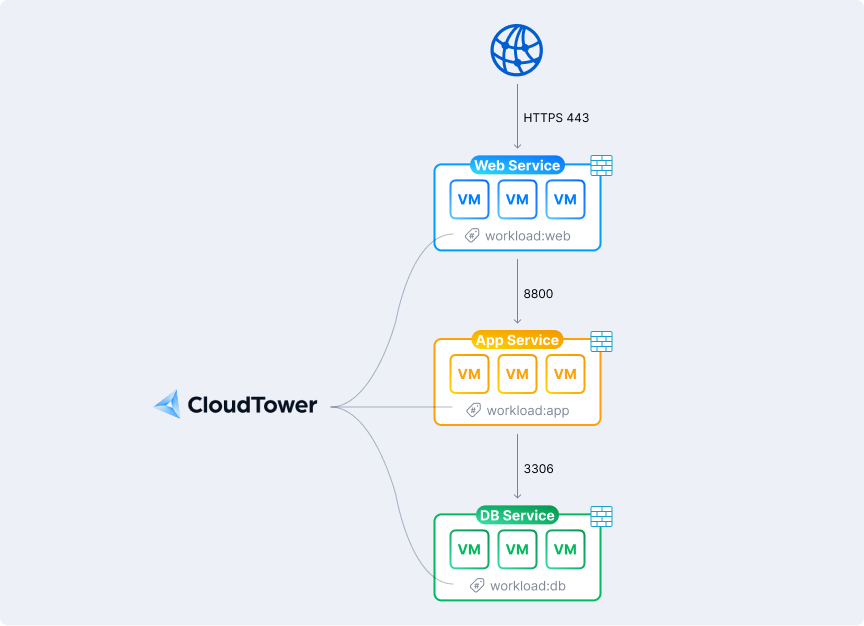
- “Zero Trust Security” among Services in Datacenter: Inter-services isolation with the finest granularity and least privilege access granted by the VM group that hosts applications, the correlation of VM group and security policies are handled by hypervisor and centralized orchestrator.
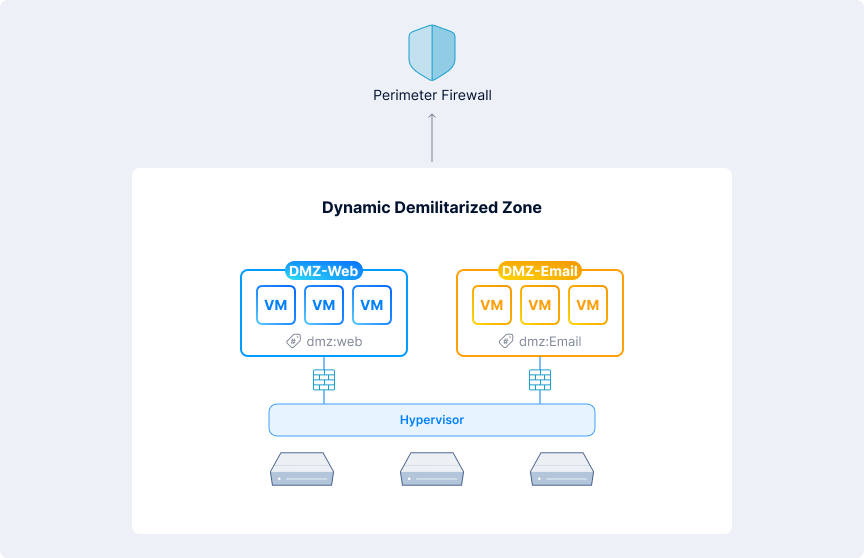
- Dynamic Demilitarized Zone: Software-defined demilitarized zone (DMZ) is created on shared resources of a datacenter to demilitarize the access to applications flexibly.
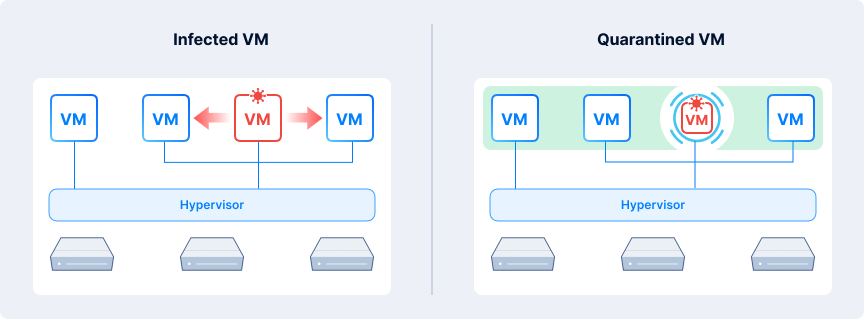
- Isolation of Abnormal Virtual Machine: Complete isolation policy is applied to abnormal virtual machines in time. Once applied, the virtual machine becomes completely isolated from other business networks and system networks, with no inbound or outbound traffic allowed, to block the proliferation of vulnerabilities.
- Security of Business Unit Grouping: Adopt flexible grouping to the application-hosting virtual machines managed and maintained by different business units, create and apply access rules and security policies for inter-group or inner-group traffic.
SMTX OS Basic Edition (and above) supports enabling the Network and Security component, it must be used in conjunction with CloudTower Basic Edition (and above). The current Network and Security component is ready for order in either subscription or perpetual license model. For easy access to a 90-day free trial of a full set of security features, please contact SmartX sales representative.
(SMTX OS is the core software of SmartX hyper-converged infrastructure, learn more about this product on https://www.smartx.com/global/smtx-os/)
About SmartX:
SmartX provides leading hyper-converged and distributed storage products to help our customers build the enterprise cloud infrastructure. Inspired by our purpose “Make IT Simple”, we are continuously innovating our products to support multiple virtualization workloads, serving industry leaders across finance, healthcare, manufacturing, retail, and real estate. Learn more about SmartX at smartx.com/global/.
